Technology
Cartetach: Understanding Its Meaning, Purpose, and Modern Use
Comprehensive guide to Cartetach—its meaning, purpose, uses, benefits, and real-world applications across creativity, learning, business, and personal organization.

Introduction
Cartetach is a word that sparks curiosity the moment you hear it. It sounds technical, yet artistic; structured, yet flexible. In this article, you’ll explore exactly what Cartetach means, how it originated, and why it’s becoming a widely discussed concept across creative, technological, educational, and organizational fields. Cartetach represents a way of organizing information, ideas, or processes in a dynamic, card-based structure—and people are embracing it because it blends clarity with creativity. By the time you finish reading, you’ll understand how Cartetach works, why it matters, and how you can apply it in real-life situations to improve productivity, learning, collaboration, and personal growth.
What Is Cartetach? A Complete Overview
Cartetach refers to a flexible, card-based system for capturing, structuring, and navigating information. Think of it as a method that transforms scattered thoughts into organized, visual blocks—almost like digital or physical cards that help you plan, build, and understand complex ideas. Because Cartetach adapts to multiple fields, people use it for project planning, storytelling, learning systems, productivity workflows, and creative development.
At its core, Cartetach blends structure with freedom. It doesn’t lock you into rigid rules; instead, it gives you the freedom to arrange and rearrange information until it makes sense. This fluid, card-style method is why Cartetach is gaining attention in both professional and personal environments.
Basic Profile of Cartetach
| Attribute | Description |
|---|---|
| Concept Type | Card-based structuring framework |
| Primary Use | Organizing ideas, tasks, processes, and learning |
| Adaptability | Highly flexible across industries |
| Origin Model | Inspired by modular systems and visual planning |
| User Base | Creators, students, professionals, educators, strategists |
Understanding the Core Principles of Cartetach
1. Modularity at Its Heart
Cartetach works like a modular grid. Each card represents a piece of information, allowing you to break large concepts into small, digestible units. This approach helps reduce overwhelm and encourages clearer thinking.
2. Visual Navigation
Humans understand visual patterns faster than long blocks of text. Cartetach uses visual placement, card grouping, and color-coded sections to help you understand relationships between ideas. This visual style supports creativity and smoother decision-making.
3. Nonlinear Thinking
Instead of forcing you to go step by step, Cartetach allows you to jump freely between connected ideas. Whether you’re brainstorming or planning, you can move through information the way your mind naturally works.
4. Continuous Adaptability
Cartetach is designed to evolve. Cards can be updated, rearranged, expanded, or archived without disrupting the overall structure. That’s why it works so well in fast-changing environments.
History and Evolution of the Cartetach Concept
Many believe Cartetach originated from early organizational systems used in libraries, research institutions, and creative studios. Over time, the concept evolved, influenced by:
- traditional index card systems
- mind mapping techniques
- project management models
- digital whiteboards
- modular design practices
The evolution of Cartetach reflects the modern need for flexible thinking. As people deal with complex information daily, the system offers simplicity without sacrificing depth.
How Cartetach Works: A Practical Explanation
Cartetach relies on three main components:
1. The Card Element
Each card holds a single idea, task, concept, or data point. This ensures clarity and avoids clutter.
2. The Board or Canvas
This is the space where all cards sit. It could be a digital screen, a notebook page, or a physical board on a wall.
3. Relationships Between Cards
You can group cards, link them, stack them, categorize them, or arrange them in sequences to create meaningful connections.
Key Components of a Cartetach System
| Component | Purpose | Example |
|---|---|---|
| Core Card | Stores the main idea or step | “Marketing Idea” |
| Category Card | Organizes related cards | “Design,” “Budget,” “Goals” |
| Link Card | Creates connections between cards | “Step 1 → Step 2” |
| Expansion Card | Adds supporting details | Notes, references |
| Priority Card | Highlights importance | High/Medium/Low |
Why Cartetach Matters in Today’s World
Cartetach shines because life and work today involve managing countless ideas, tasks, and pieces of information. This system reduces chaos by breaking things into Manageable units. It helps you:
- think clearly
- create structure
- stay focused
- build sustainable workflows
- enhance creativity
Whether you’re a student organizing a study plan or a business leader mapping a strategy, Cartetach provides a universal structure to streamline thinking.
Applications of Cartetach Across Multiple Fields
Cartetach isn’t limited to one industry. It adapts smoothly across many areas because of its flexible nature.
Cartetach in Creative Work
Writers, designers, filmmakers, and artists love Cartetach because it brings clarity to the creative process. A filmmaker can outline scenes using cards; a designer can plan layout ideas; a writer can build character arcs and chapters. The card-based structure reduces creative block and opens the door to imaginative exploration.
Cartetach in Education and Learning
Students often struggle with complex subjects. Cartetach breaks them into smaller concepts, making learning more manageable. Teachers also use it to design lessons, visualize curriculum, or encourage active participation.
For example, a high school science teacher may use Cartetach to explain ecosystems. Each card represents a part of the ecosystem, letting students visually map interactions.
Cartetach in Personal Productivity
People use Cartetach in daily routines to manage priorities. It supports many personal workflows, such as:
- time management
- habit tracking
- goal planning
- journaling
- decision-making
Because the system adapts naturally to individual preferences, it’s especially useful for teens and adults who want to build better habits without pressure.
Cartetach for Business and Teams
Teams apply Cartetach to:
- plan projects
- map workflows
- structure meetings
- assign responsibilities
- solve problems collaboratively
Each team member can contribute cards, rearrange ideas, or visualize the plan together. This removes confusion and builds shared understanding.
Cartetach for Research and Knowledge Building
Researchers use Cartetach to collect data, connect theories, outline experiments, and record findings. It becomes a living knowledge map that grows as research expands.
Real-World Examples of Cartetach in Action
Example 1: Storytelling Workflow
A novelist divides her book into cards: characters, settings, conflicts, scenes. She rearranges them until the plot flows perfectly.
Example 2: Business Strategy Map
A startup founder uses Cartetach to categorize goals into product development, marketing, finance, customer experience, and team building.
Example 3: Learning a New Skill
A student uses cards to learn coding, creating sections such as basic concepts, exercises, challenges, and mistakes to avoid.
How to Build Your First Cartetach Board
Step 1: Define Your Main Objective
Choose a theme or goal for the board. For example, plan a project or organize your ideas.
Step 2: Create Core Cards
Write down your biggest ideas on individual cards.
Step 3: Group and Label
Sort your cards into categories so the information becomes clearer.
Step 4: Connect and Expand
Add supporting cards, connect related ideas, or rearrange them to form a strong structure.
Step 5: Refine Continuously
As ideas grow, update your Cartetach board. That’s the beauty of its flexibility.
Strengths and Limitations of Cartetach
Strengths
| Feature | Benefit |
|---|---|
| Flexible structure | Works for any niche |
| Easy to update | Adapts to changes |
| Visual clarity | Enhances understanding |
| Encourages creativity | Supports open thinking |
Limitations
- Can become overwhelming if overused
- Requires consistent maintenance
- Needs clear objectives for best results
Advanced Uses of Cartetach
Cartetach can also support:
Strategic Foresight
Organizations use it to visualize future scenarios and risks.
Mental Mapping
Therapists and wellness coaches may use card-based approaches to help individuals understand thoughts or emotions.
Problem-Solving Models
Engineers and analysts apply Cartetach to break down technical challenges into solvable steps.
How Cartetach Helps People Think Better
Because Cartetach respects the natural flow of human thought, it improves:
- memory
- comprehension
- organization
- creativity
- productivity
It transforms complex topics into clear structures, giving you mental breathing room to grow and explore.
Conclusion
Cartetach is more than a planning method—it’s a powerful approach to thinking, learning, and creating. Its card-based structure gives you Freedom without losing clarity, allowing you to visualize ideas, adapt quickly, and build strong connections between concepts. Whether you’re a student, creator, professional, or someone simply looking to bring order to your ideas, Cartetach offers a flexible and effective framework that grows with you. By adopting this method, you gain a tool that not only organizes information but also strengthens imagination, decision-making, and personal development.
Frequently Asked Questions (FAQs)
1. What is Cartetach used for?
Cartetach is used for organizing ideas, planning projects, learning new concepts, and visualizing complex information through card-based structures.
2. Is Cartetach only for professionals?
Not at all. Students, creators, and everyday users benefit from Cartetach because it adapts to personal and professional needs.
3. Can Cartetach be used digitally and physically?
Yes. You can create Cartetach boards using apps, digital whiteboards, notebooks, or physical cards—whatever fits your style.
4. Why is Cartetach becoming popular?
People love it because it simplifies complexity, encourages creativity, and works well across education, business, and personal organization.
5. How do I start using Cartetach?
Begin with a clear goal, create core cards for main ideas, group them into categories, and expand the board as your understanding grows.
Technology
Grantorrent: What It Is and What Users Should Know
Learn what Grantorrent is, how torrent platforms work, legal risks, safety concerns, and safer alternatives in this in-depth guide.
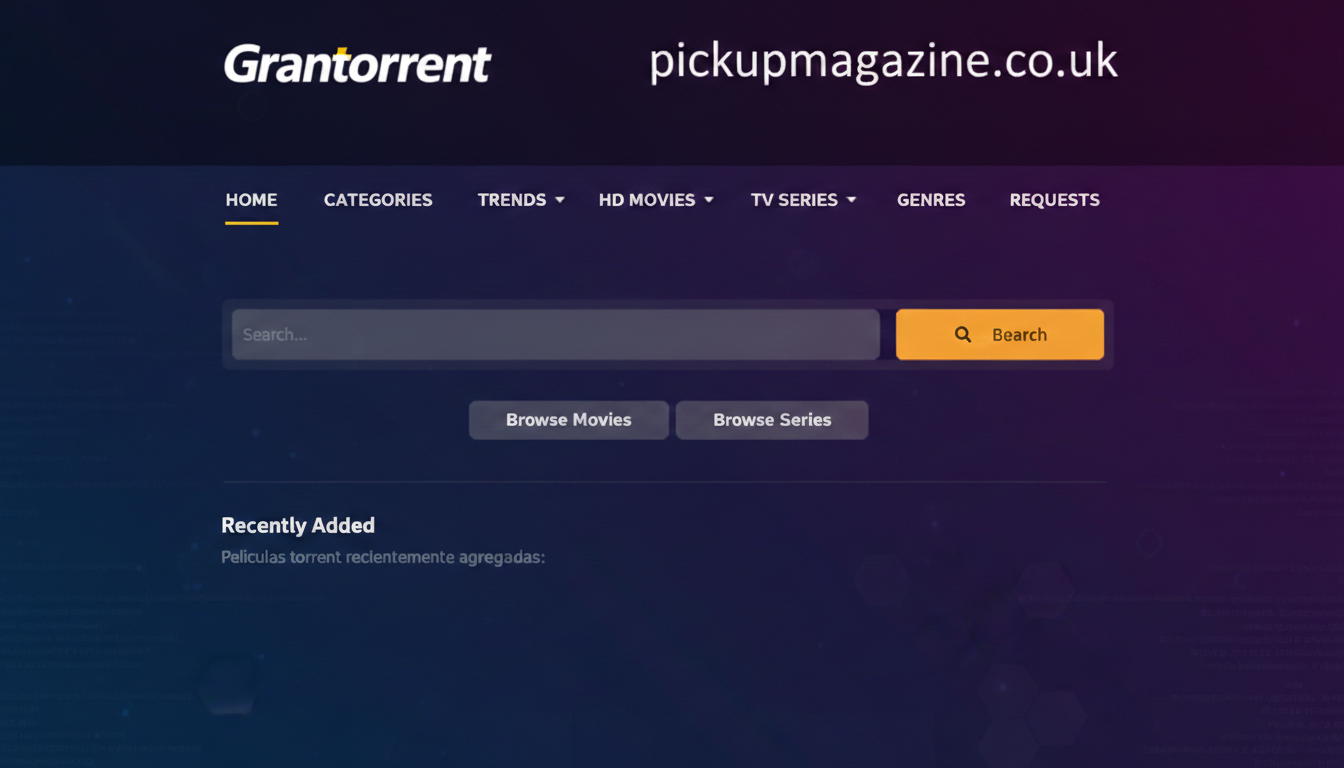
Introduction
In today’s digital world, platforms like Grantorrent spark curiosity, debate, and strong opinions. Whether someone stumbles across the name while searching for downloadable content or hears it mentioned in online communities, the first question is simple: what exactly is Grantorrent, and why does it matter? The answer isn’t just about files or technology. It’s about digital access, responsibility, safety, and informed choices.
This comprehensive guide explores Grantorrent from every angle. You’ll learn how torrent-based platforms work, what attracts users to them, the legal and ethical considerations involved, and the risks that often go unnoticed. We’ll also compare alternatives, examine user behavior trends, and provide practical advice to help you navigate the digital landscape safely. By the end, you’ll have a well-rounded understanding of Grantorrent and its broader implications.
Understanding Grantorrent as a Torrent-Based Platform
Grantorrent is generally associated with torrent file sharing, a peer-to-peer (P2P) technology that allows users to download and upload files simultaneously. Unlike traditional Downloads, which rely on a single server, torrent systems distribute file pieces across multiple users. This decentralized structure makes file sharing fast and efficient.
To better understand Grantorrent, it helps to break down how torrent systems operate:
| Feature | Description |
|---|---|
| Peer-to-Peer (P2P) | Files are shared directly between users |
| Torrent File | A small file containing metadata for downloads |
| Seeder | A user who uploads or shares the full file |
| Leecher | A user who downloads file pieces |
| Tracker | Coordinates communication between peers |
The appeal of platforms like Grantorrent lies in accessibility. Users can find movies, software, music, books, and other digital assets in one place. However, convenience often overshadows critical questions about legality, safety, and ethical responsibility.
Torrent technology itself isn’t illegal. It was originally designed to reduce server strain and improve file distribution. The issue arises when copyrighted material is shared without permission.
Why Platforms Like Grantorrent Attract Users
People don’t gravitate toward torrent platforms by accident. There are clear motivations behind their popularity.
Accessibility and Cost
Many users turn to torrent platforms because they want free access to premium content. Subscription fatigue is real. Streaming services, software licenses, and digital tools can add up quickly. For some users, torrent sites appear to offer a shortcut around these costs.
However, “free” often carries hidden consequences.
Availability of Rare or Archived Content
Another major draw is access to hard-to-find files. Older films, discontinued software, or out-of-print books may not be easily available on mainstream platforms. Torrent communities sometimes preserve digital content that has otherwise vanished.
This archival aspect gives platforms like Grantorrent a certain underground appeal. Still, preservation doesn’t automatically equal permission.
Speed and Decentralization
Because torrent systems distribute files across multiple peers, downloads can be fast when many seeders are active. This efficiency makes large files manageable.
But speed doesn’t eliminate risk.
Legal Considerations Surrounding Grantorrent
One of the most critical aspects of using platforms like Grantorrent involves legal implications. The legality of torrenting depends entirely on what is being shared.
Legal vs. Illegal Torrenting
Here’s a simplified comparison:
| Type of Content | Legal Status |
|---|---|
| Open-source software | Legal |
| Public domain films | Legal |
| Copyrighted movies without permission | Illegal |
| Cracked software | Illegal |
| Licensed digital books shared freely | Illegal |
Downloading copyrighted material without authorization violates intellectual property laws in many countries. Penalties can range from warning notices to fines or even legal action.
Different jurisdictions enforce laws differently, but the risk remains significant.
Ethical Responsibility
Even when enforcement seems inconsistent, ethical considerations remain important. Creators invest time, money, and effort into producing digital content. Unauthorized distribution undermines their revenue and sustainability.
For example, independent filmmakers often rely heavily on legitimate sales. Widespread torrenting can severely impact their income. Supporting creators through legal channels ensures continued innovation and production.
Safety Risks Associated With Grantorrent
Beyond legal concerns, security risks are equally serious.
Malware and Viruses
Torrent files can be disguised. A movie download might contain malicious software. Hackers frequently embed malware within popular file names to lure users.
Some common risks include:
- Ransomware that locks your files
- Spyware that steals login credentials
Even experienced users can fall victim. Antivirus software helps, but it’s not foolproof.
Data Exposure
Torrenting exposes your IP address to other peers in the network. This means your online activity may be visible to others. Privacy concerns are significant, especially in regions with strict enforcement policies.
Fake Files and Scams
Not all files on torrent platforms are legitimate. Some are incomplete, corrupted, or deliberately misleading. Users might waste time downloading useless files or fall into scam traps.
How Grantorrent Reflects Broader Digital Trends
Grantorrent doesn’t exist in isolation. It reflects a larger shift in digital consumption habits.
The Demand for Instant Access
Modern users expect instant gratification. Waiting weeks for physical media feels outdated. Torrent platforms align with this demand for immediate digital access.
However, streaming services and cloud platforms have begun addressing this need legally. This shift challenges the long-term relevance of unauthorized torrent sites.
Subscription Fatigue and Platform Fragmentation
As entertainment becomes fragmented across multiple subscription platforms, some users feel overwhelmed. Instead of paying for five services, they look for centralized alternatives.
Grantorrent-style platforms appear to offer that simplicity. Yet, the trade-off involves risk and ethical compromise.
Alternatives to Grantorrent for Legal Access
For users seeking safer options, many legitimate alternatives exist.
Streaming and Digital Platforms
Services like Netflix, Spotify, Amazon Prime, and Apple Books provide extensive libraries. While subscriptions cost money, they eliminate legal and security concerns.
Many platforms also offer:
- Free trials
- Student discounts
- Ad-supported free tiers
These options reduce financial barriers significantly.
Open-Source and Public Domain Resources
Public domain libraries host thousands of free books and films legally. Open-source software communities provide robust tools without licensing fees.
Here’s a comparison:
| Platform Type | Risk Level | Cost | Legality |
|---|---|---|---|
| Torrent Sites | High | Free | Often Illegal |
| Subscription Services | Low | Paid | Legal |
| Public Domain Libraries | Very Low | Free | Legal |
| Open-Source Platforms | Very Low | Free | Legal |
Legal options not only protect users but also support content creators.
The Technology Behind Torrent Systems
To fully understand Grantorrent, it helps to examine the technical mechanics.
Torrent systems break files into small pieces. These pieces download simultaneously from different users. Once a user finishes downloading, they can begin seeding, contributing back to the network.
This distributed model reduces server costs and bandwidth strain. It’s efficient and scalable.
Interestingly, some companies use similar decentralized methods for legitimate file distribution. For example, game developers may use peer-assisted delivery to reduce load during large updates.
The technology itself is neutral. Its usage defines its legality.
Real-World Example: A User Experience Scenario
Consider this hypothetical scenario.
Alex wants to download a newly released film without paying for a streaming subscription. He finds it listed on a torrent platform similar to Grantorrent. The file downloads quickly, but hidden inside is malware that captures his banking credentials.
A few days later, fraudulent charges appear on his account. What seemed like a shortcut becomes an expensive lesson.
This example highlights a broader truth: digital convenience often carries unseen costs.
Ethical Digital Citizenship
Digital citizenship goes beyond simply following laws. It involves understanding how online actions affect others.
Creators rely on legitimate revenue streams. Developers depend on software licensing. Musicians earn from streaming royalties. When users bypass legal channels, it disrupts entire ecosystems.
Supporting legal distribution ensures creative industries remain sustainable.
Should You Use Grantorrent?
This question depends on awareness and responsibility.
If the content being downloaded is public domain or open-source, torrenting may be perfectly legal. However, if the content is copyrighted without permission, risks increase dramatically.
Users should ask:
- Is this content legally shareable?
- Am I exposing my device to malware?
- Am I respecting the creator’s rights?
Informed decisions protect both users and creators.
The Future of Platforms Like Grantorrent
The future of torrent-based platforms is uncertain. Increased enforcement, improved legal alternatives, and shifting user behavior are reshaping the landscape.
Cloud storage and streaming continue to dominate. Content creators are also experimenting with new distribution models, including direct-to-consumer platforms and blockchain-based ownership systems.
While torrent technology won’t disappear, its role may continue to evolve.
Conclusion
Grantorrent represents more than just a file-sharing name. It reflects modern digital behavior, access Expectations, and the tension between convenience and responsibility. Torrent technology itself is innovative and efficient, but its misuse creates legal and ethical complications.
Throughout this article, we explored how Grantorrent works, why users are drawn to it, the legal implications involved, and the security risks that often go unnoticed. We also compared safer alternatives and examined broader industry trends.
The takeaway is simple: informed decisions matter. Choose legal platforms whenever possible. Protect your devices. Respect creative work. Digital freedom works best when paired with responsibility.
Frequently Asked Questions (FAQs)
1. Is Grantorrent legal to use?
It depends on the content being downloaded. Sharing or downloading public domain material is legal, but copyrighted content without permission is illegal in most countries.
2. Can using Grantorrent harm my computer?
Yes. Torrent platforms may host files containing malware, ransomware, or spyware that can compromise your device and personal data.
3. Why do people use torrent platforms like Grantorrent?
Users are often drawn by free access, rare content availability, and fast download speeds offered through peer-to-peer networks.
4. Is torrent technology itself illegal?
No. Torrent technology is legal. It becomes illegal only when used to distribute copyrighted material without authorization.
5. What are safer alternatives to Grantorrent?
Legal streaming services, public domain libraries, and open-source software platforms offer secure and authorized access to digital content.
Technology
Bigtakip.net: A Deep Dive into Social Growth
Discover what Bigtakip.net is, how it works, its benefits, risks, and smarter strategies for sustainable social media growth.

Introduction
The digital world moves fast. One viral post can change a life overnight, while months of effort can disappear in silence. In that intense environment, platforms like Bigtakip.net have gained attention from creators, influencers, entrepreneurs, and even small businesses looking to grow their online presence. But what exactly is Bigtakip.net? How does it work? And more importantly, is it worth your time and trust?
In this comprehensive guide, we’ll explore everything you need to know about Bigtakip.net—from how it functions and who uses it, to its potential benefits, risks, ethical considerations, and smarter strategies for long-term digital growth. Whether you’re a content creator, brand owner, freelancer, or simply curious, this article will give you practical insights you can actually use.
What Is Bigtakip.net?
At its core, Bigtakip.net is a social media growth platform. It offers services designed to increase metrics such as followers, likes, views, and engagement across popular social media networks.
These types of platforms typically promise fast results. For someone trying to break through online noise, that promise can feel irresistible. After all, visibility often influences credibility. When people see higher numbers, they’re more likely to pay attention.
Below is a quick informational overview of the platform type:
| Feature Category | Details |
|---|---|
| Platform Type | Social media growth service |
| Primary Purpose | Increase followers and engagement metrics |
| Target Users | Influencers, brands, small businesses |
| Access Model | Website-based ordering system |
| Growth Method | Automated or network-based interaction |
While exact service models may vary, platforms like Bigtakip.net usually operate through automated systems or large user networks to boost engagement numbers.
Why Platforms Like Bigtakip.net Attract Users
Let’s be honest—numbers matter online. They influence perception. A profile with 50,000 Followers instantly feels more authoritative than one with 500.
The Psychology Behind Social Proof
Humans are wired to follow the crowd. If thousands of people follow an account, others assume it must be valuable. This psychological phenomenon is called social proof.
For new creators, building that first wave of momentum can feel impossible. That’s where services like Bigtakip.net step in. They offer a shortcut to perceived popularity.
However, perception and genuine influence are two different things. That’s an important distinction we’ll revisit later.
Competitive Digital Landscape
Social platforms are crowded. Millions of posts go live every day. Even high-quality content can struggle without initial visibility.
Imagine opening a coffee shop on a busy street. If your place looks empty, people hesitate to walk in. But if it appears lively, others feel more confident entering. Bigtakip.net essentially aims to create that “busy café” effect for digital profiles.
How Bigtakip.net Works
Although each growth service may differ slightly, the general structure tends to follow a similar process.
Account Selection and Service Choice
Users typically choose:
- The platform (e.g., Instagram, TikTok, Twitter)
- The service type (followers, likes, views)
- The quantity desired
Orders are placed directly through the website interface.
Automated or Network-Based Engagement
The growth may come from:
- Automated systems
- Engagement exchange networks
- Real accounts incentivized to interact
The mechanics behind Bigtakip.net are often designed to deliver quick numerical increases rather than organic community building.
Benefits of Using Bigtakip.net
While controversial, there are reasons people turn to these platforms.
1. Faster Visibility
If someone is launching a new brand or campaign, a boosted profile may look more established. First impressions matter, especially in influencer marketing.
2. Confidence Boost for Creators
Early growth can motivate creators to continue producing content. Seeing engagement—even if partially assisted—can feel encouraging.
3. Perceived Credibility
Some brands and advertisers look at follower count as a preliminary filter. A higher number may open doors to conversations that otherwise wouldn’t happen.
Here’s a simplified comparison:
| Organic Growth | Growth via Services Like Bigtakip.net |
|---|---|
| Slower initial progress | Rapid numerical increase |
| Highly engaged audience | Mixed engagement quality |
| Strong long-term trust | Perception-driven influence |
| Sustainable community | Metric-focused growth |
That said, the benefits often depend on how the service is used—and whether it’s part of a broader strategy.
Risks and Considerations
No platform is perfect. And Bigtakip.net is no exception.
Platform Policy Violations
Many social networks discourage artificial engagement practices. If detected, accounts could face restrictions or penalties.
It’s important to understand the rules of each platform before using any growth service.
Engagement Quality
High follower numbers don’t always translate to meaningful interaction. If followers aren’t genuinely interested in your content, your posts may receive low engagement relative to audience size.
That imbalance can raise red flags for brands and audiences alike.
Long-Term Brand Impact
Authenticity matters more than ever. Audiences are increasingly savvy. If they sense artificial inflation, trust can erode quickly.
Think of it like inflating a balloon with hot air. It looks big, but it’s fragile. One small puncture, and it collapses.
Who Typically Uses Bigtakip.net?
The user base for platforms like Bigtakip.net often includes:
| User Type | Primary Goal |
|---|---|
| New Influencers | Kickstart audience growth |
| Small Businesses | Increase brand visibility |
| Musicians/Artists | Boost streaming or profile numbers |
| E-commerce Sellers | Enhance product credibility |
| Personal Brands | Improve first impressions |
For example, a fashion startup launching a new collection might use Bigtakip.net to make its Instagram page appear more established before running paid ads.
However, the real test comes after that initial boost. Without strong content and consistent engagement, growth often plateaus.
Ethical and Strategic Perspectives
Using services like Bigtakip.net raises an important question: Is it ethical?
The Authenticity Debate
Some argue that artificially boosting numbers is misleading. Others see it as marketing—no different from paid promotions or advertising.
The key distinction lies in transparency and intent.
If growth services are used as a temporary visibility push while focusing on real value creation, some consider it a marketing tactic. If used to deceive audiences or partners, it becomes problematic.
Smart Hybrid Approach
A more balanced strategy might include:
- Creating high-quality, audience-focused content
- Collaborating with micro-influencers
- Engaging consistently with followers
- Using promotional tools responsibly
In that scenario, Bigtakip.net becomes one small tool—not the entire foundation.
Alternatives to Metric-Driven Growth
Instead of relying solely on services like Bigtakip.net, consider long-term community building.
Storytelling Over Numbers
People connect with stories, not statistics. A creator with 2,000 deeply engaged followers often outperforms someone with 50,000 passive ones.
For example, a fitness coach sharing real transformation stories may build stronger loyalty than someone focused purely on numbers.
Consistency Builds Trust
Consistency creates recognition. Recognition builds familiarity. Familiarity builds trust.
It’s slower. But it’s solid.
Data-Driven Content Refinement
Analyzing audience preferences and adjusting content strategy can lead to sustainable growth without artificial boosts.
Think marathon, not sprint.
Real-World Case Study: Short-Term vs. Long-Term Impact
Consider two hypothetical creators:
Creator A uses Bigtakip.net to jump from 1,000 to 20,000 followers in a month.
Creator B grows organically from 1,000 to 5,000 followers in six months.
After one year:
- Creator A struggles with low engagement and inconsistent brand deals.
- Creator B secures partnerships due to high interaction rates and loyal followers.
The lesson? Numbers open doors. But engagement keeps them open.
How to Use Growth Services Responsibly
If someone chooses to use Bigtakip.net, strategic caution matters.
Limit reliance. Don’t inflate metrics beyond what engagement can realistically support. Continue prioritizing real audience connection.
Think of it as scaffolding during construction. It supports the building temporarily. But the foundation must still be strong.
The Bigger Picture: What Really Drives Online Success
Success online isn’t just about visibility. It’s about:
- Value
- Authenticity
- Consistency
- Community
- Adaptability
Platforms evolve. Algorithms change. Trends fade. But genuine connection remains powerful.
Whether someone uses Bigtakip.net or not, long-term growth always depends on meaningful content and audience trust.
Conclusion
Bigtakip.net represents a growing category of digital growth platforms that promise fast visibility in a highly competitive online world. For new creators and businesses, that initial boost can feel like a lifeline. It can create perceived credibility, improve first impressions, and even spark momentum.
However, numbers alone don’t equal influence. Sustainable success requires authentic Engagement, valuable content, and long-term strategy. Used carelessly, metric-focused growth can damage trust. Used cautiously as part of a broader plan, it may offer short-term advantages.
The smartest approach blends visibility tactics with genuine community building. Focus on creating real value first. Let growth support your mission—not define it.
In the end, meaningful digital presence isn’t built overnight. It’s built with intention.
Frequently Asked Questions (FAQs)
1. What is Bigtakip.net used for?
Bigtakip.net is typically used to increase social media metrics such as followers, likes, and views. It aims to boost profile visibility quickly.
2. Is Bigtakip.net safe to use?
Safety depends on platform policies and how responsibly it’s used. Users should understand the terms of the social networks they operate on.
3. Does using Bigtakip.net guarantee real engagement?
Not necessarily. Higher numbers don’t always translate to meaningful audience interaction or long-term loyalty.
4. Can Bigtakip.net help small businesses?
It may improve first impressions, but sustainable growth still requires strong branding and consistent content creation.
5. What is the best alternative to artificial growth?
Building authentic relationships, sharing valuable content, and engaging consistently with your audience are the most reliable long-term strategies.
Technology
Uac3600816: Meaning, Uses, and Why It Appears Online
Learn what Uac3600816 means, why it appears in systems, and how to interpret this identifier safely across logs, records, and online platforms.

Introduction
If you’ve recently come across the code Uac3600816, you’re probably wondering what it actually means and why it keeps showing up in certain systems, logs, online platforms, or digital records. The truth is, identifiers like Uac3600816 are often not random—they usually serve a specific purpose in tracking, categorizing, or referencing something inside a database or automated system. Whether you found it in an error message, a device log, an online report, or a file reference, Uac3600816 can feel confusing because it doesn’t look like a typical word, product name, or standard serial number. But that’s exactly what makes it important to understand.
In this detailed guide, we’ll break down what Uac3600816 might represent, where codes like this typically come from, why people search for them, and how you can interpret them intelligently. By the end, you’ll know how to approach such identifiers with confidence instead of confusion.
Quick Overview Table: Uac3600816 Explained
Before we go deep, here’s a quick informational table that summarizes what Uac3600816 may represent in practical terms.
| Category | Possible Meaning |
|---|---|
| Code Type | Identifier / tracking code |
| Common Use | Logs, records, system references |
| Likely Source | Software system, database, device firmware |
| User Intent | Identify meaning, fix errors, confirm authenticity |
| Visibility | Appears in technical or automated contexts |
| Format Style | Alphanumeric reference code |
This quick table helps set expectations: Uac3600816 is likely a system-generated identifier, not a name meant for casual users.
What Is Uac3600816?
The code Uac3600816 appears to be an alphanumeric identifier used in a structured environment such as software systems, digital tracking platforms, or automated reporting tools. Codes like this are commonly generated for internal reference purposes. They are often created to label something unique—such as a user account, a file entry, a transaction, a product batch, or an internal event.
Unlike product names or customer-facing labels, identifiers like Uac3600816 are designed for machines and databases. That’s why they feel “meaningless” at first glance. However, they often carry hidden structure, and their value comes from how they connect information behind the scenes.
In many systems, a code like Uac3600816 works like a fingerprint. It helps software identify one item from millions without confusion.
Breaking Down the Structure of Uac3600816
The “Uac” Prefix
The first part of the code—Uac—looks like a prefix. Prefixes are common in technical systems because they provide quick categorization. Instead of storing every item in one massive list, systems group entries by prefixes.
In many cases, a prefix like Uac might stand for something such as:
- User Access Code
- Unified Account Code
- User Authentication Code
- Unique Activity Code
- Utility Access Component
It’s important to understand that the exact meaning depends entirely on where the code is being used. Still, the presence of “Uac” strongly suggests the code is connected to access, authorization, or a user-related category.
The Numeric Portion: 3600816
The numeric portion—3600816—likely functions as the unique identifier. It could represent:
- a sequential number
- a timestamp-based code
- a database entry ID
- a generated random ID
- a batch or ticket number
This is the part that usually ensures uniqueness. Systems rely on numbers like this to avoid duplication.
Why Does Uac3600816 Appear in Systems?
Digital Systems Need Unique References
Modern software handles massive volumes of data. Even small apps store thousands of records. Without unique identifiers, everything becomes messy. Imagine a system storing customer data without unique IDs—two people with the same name could easily get mixed up.
That’s why codes like Uac3600816 exist. They prevent confusion, ensure accurate tracking, and help systems retrieve exact records instantly.
It May Be Linked to a Hidden Record
One reason Uac3600816 becomes visible to users is when a system accidentally exposes internal IDs. This can happen when:
- an error occurs
- a report exports raw data
- a broken link displays an ID
- a database entry is referenced directly
- a system uses internal IDs in URLs
When these codes appear publicly, users naturally search for them, hoping to understand what they mean.
Common Places Where Uac3600816 Might Show Up
Error Messages and Technical Logs
One of the most common places people see Uac3600816 is inside system logs or error messages. When software fails, it often outputs internal reference IDs to help developers trace the issue.
For example, a system might display something like:
“Error: Record not found (Uac3600816).”
This doesn’t mean the user did something wrong. It usually means the system is pointing to a missing or inaccessible entry.
File or Document References
Some systems assign codes like Uac3600816 to documents, uploads, or files stored in their database. This is common in:
- cloud storage systems
- enterprise record systems
- government filing portals
- finance-related applications
- customer service ticket systems
A document might be stored with a name users see, but internally it could be labeled Uac3600816.
Security or Access Control Systems
The prefix “Uac” strongly suggests the possibility of access control. Many authentication systems generate identifiers for user sessions, login attempts, or permission roles.
If Uac3600816 appears during a login issue or access request, it may be linked to a session token or access entry in a security database.
Table: Possible Meanings of Uac3600816 by Context
This table explains how the meaning changes depending on where you found the code.
| Where You Found It | Likely Meaning of Uac3600816 |
|---|---|
| Login Screen | User access/session identifier |
| App Error Message | Reference ID for debugging |
| Database Export | Record ID for an entry |
| Website URL | Internal page or file identifier |
| Customer Support Ticket | Ticket or case tracking number |
This shows why context matters. The same code can mean different things depending on the platform using it.
Is Uac3600816 a Virus or Dangerous Code?
Why People Assume It’s Malware
When users see unfamiliar codes, the first thought is often fear. It’s understandable. Codes like Uac3600816 can resemble malware file names, suspicious processes, or hidden trackers.
However, in most cases, identifiers like this are harmless. They are simply part of a structured system.
That said, the code could appear in malicious contexts if it is being used as a tracking identifier by a suspicious site or file. The code itself isn’t dangerous—but the environment where you found it could be.
How to Judge Risk Properly
To determine whether Uac3600816 is harmless or suspicious, ask yourself:
- Did it appear in a trusted app or website?
- Was it part of an official report or document?
- Did it appear after downloading unknown software?
- Did your device behave strangely afterward?
If it appeared in a professional system or legitimate platform, it’s most likely safe. If it appeared after a suspicious download, it may be worth checking your system for threats.
Uac3600816 and the Role of Tracking Codes
Tracking Codes Are Everywhere
Tracking codes are not limited to finance or technology companies. They exist in almost every modern system:
- delivery tracking numbers
- airline reservation codes
- hospital patient record IDs
- support ticket numbers
- payment reference IDs
Uac3600816 fits into this same family of identifiers. The only difference is that it looks more technical than user-friendly.
Why Systems Use Codes Instead of Names
Names are unreliable. They can be duplicated, misspelled, or changed. A code like Uac3600816 never changes unless the system modifies it intentionally.
This is why databases love codes. They are stable and predictable.
Table: Codes Like Uac3600816 Compared to Common Identifiers
| Identifier Type | Example | User-Friendly? | Purpose |
|---|---|---|---|
| Tracking Number | 1Z999AA10123456784 | Medium | Shipment tracking |
| Ticket ID | CASE-1129 | High | Support reference |
| Internal Code | Uac3600816 | Low | Database/system reference |
| Transaction ID | TXN-9002341 | Medium | Payment verification |
This comparison shows that Uac3600816 is likely an internal code rather than a consumer-facing one.
Why Uac3600816 Becomes a Search Topic
People Want Clarity and Control
When users see Uac3600816, they want to know if it affects them. They may worry about account security, device issues, or unknown transactions.
This is a natural response. In a digital world, unclear identifiers feel like hidden threats.
It May Be Linked to a Missing Page or Broken Link
Sometimes a user searches for Uac3600816 because it appears in a URL. A page may redirect to something like:
/record/Uac3600816
If that page fails to load, users assume something went wrong and search the code to find answers.
Practical Steps to Investigate Uac3600816
Step 1: Check Where You Found It
The first step is always context. Was it in:
- an email?
- a browser link?
- a system log?
- an app notification?
This determines whether it’s technical, administrative, or suspicious.
Step 2: Look for Associated Text
Most codes appear alongside clues. For example:
- “User ID: Uac3600816”
- “Document reference: Uac3600816”
- “Access denied: Uac3600816”
These surrounding words reveal what category the code belongs to.
Step 3: Search Within the Same Platform
If you found Uac3600816 in a platform, try searching it within that same platform. Many dashboards allow internal searching. It may lead to a record, case file, or transaction.
Step 4: Contact Support if It’s Critical
If the code appears in something financial, legal, or security-related, the safest move is to contact official support and provide the code. Support teams use identifiers like Uac3600816 to locate records quickly.
Case Study Example: When Codes Like Uac3600816 Matter
Imagine you apply for a service online. You receive a message saying:
“Your application could not be processed. Reference: Uac3600816.”
You might panic. But this code is likely used by the system to identify your application attempt. Support can look it up, see what went wrong, and fix the issue.
In this case, Uac3600816 is not a threat. It’s a troubleshooting tool.
This is why such identifiers are valuable, even when confusing.
The Human Side of Machine Codes
Why These Codes Feel Unfriendly
Codes like Uac3600816 feel cold because they aren’t designed for humans. They’re built for systems that don’t need emotional comfort, clear language, or explanation.
But users are human. They need reassurance and clarity.
That mismatch is why these codes often trigger anxiety.
Why Understanding Them Helps
Once you understand that Uac3600816 is likely just an internal reference, it becomes less scary. It turns into something practical: a clue, a label, a breadcrumb.
Knowledge reduces uncertainty, and uncertainty is what causes fear.
Uac3600816 in Digital Administration and Automation
Automation Generates More Codes Than Ever
As companies automate their operations, internal identifiers multiply. Every form submission, upload, and transaction generates a reference code.
So it’s completely normal to see strange codes today. In fact, the more digital a platform becomes, the more likely you are to encounter identifiers like Uac3600816.
The Future Will Bring Even More Identifiers
As artificial intelligence, automation, and digital security expand, codes will become even more common. Many people will encounter these identifiers daily without realizing it.
Uac3600816 is part of this larger digital reality.
Conclusion
The identifier Uac3600816 may look mysterious at first, but it is most likely a system-generated code used for tracking, database organization, or access-related recordkeeping. Whether it appears in a login issue, error message, document reference, or Internal URL, its purpose is usually practical rather than dangerous. Throughout this article, we explored how Uac3600816 might be structured, why it appears in digital systems, and how to interpret it responsibly. The key takeaway is simple: don’t panic when you see codes like this. Instead, focus on context, look for surrounding clues, and use the identifier as a tool for understanding what’s happening. With the right approach, Uac3600816 becomes less of a mystery and more of a useful reference point.
Frequently Asked Questions (FAQs)
What is Uac3600816?
Uac3600816 is likely a system-generated identifier used to track a record, user session, file, or database entry.
Why does Uac3600816 appear in error messages?
It may appear as a reference code that helps developers or support teams locate the exact issue in a system log.
Is Uac3600816 a virus or malware?
The code itself is not a virus, but if it appears in a suspicious environment, you should investigate the source carefully.
Can I trace Uac3600816 to a specific person or account?
Usually, only the platform that generated the code can trace it, since it is tied to internal database records.
What should I do if I keep seeing Uac3600816?
Check the context where it appears, look for related messages, and contact the platform’s support team if it involves security or transactions.
-

 Celebrity3 weeks ago
Celebrity3 weeks agoMark Redknapp: The Life, Family And Journey Behind The Famous Name
-

 Celebrity3 weeks ago
Celebrity3 weeks agoBen Shephard Wife Illness: The Truth, Timeline, and What We Know Today
-

 Celebrity3 weeks ago
Celebrity3 weeks agoCarrie Schenken: A Private Life, Public Curiosity, and Lasting Partnership
-

 Celebrity3 weeks ago
Celebrity3 weeks agoLinford Christie Wife: Untold Facts, Personal Life & Truth Behind the Legend
-

 Celebrity3 weeks ago
Celebrity3 weeks agoDenika Kisty: Life, Legacy, and Strength Beyond Fame
-

 Celebrity3 weeks ago
Celebrity3 weeks agoHenry Zeffman Partner: What We Know About His Private Life and Relationships
-

 Celebrity3 weeks ago
Celebrity3 weeks agoLesa Tureaud: Identity, Legacy, and a Life of Purpose
-

 Celebrity3 weeks ago
Celebrity3 weeks agoKelly Frayne: A Complete Guide to Her Life, Career, and Growing Public Interest
